Calling For A New HTTPS-Certification process
We all agree – HTTPS – the encrypted communication between WWW-browsers and servers – usually makes sense. However – under the cover of secure communications, some folks have silently pushed their version of rules into our life. And that makes things complicated – to say the least.
Just a short introduction to HTTPS: If you want to run a server that provides secure communications, you need to create a certificate. This certificate gives the connecting browsers the necessary encryption keys so that a safe connection can be established. That could be the end of the story. But people added another feature into the mix: Trust. Basically – your certificate tells the browser that the encryption keys provided are for a specific domain name, say “thisdomain.com”. So how does the browser know that you are “thisdomain.com” ? You have to prove it to a third party. You have to convince a so called “certificate authority” that you are in control of the domain.
Here’s the thing – regular Internet users or even companies have no say in this. Given the growing importance of SSL/TLS (the technology behind HTTPS) – it’s disturbing that just a few companies set the rules we have to follow.
Why is this a problem? Because those companies can arbitrarily decide that some users, domains or other criteria can’t get certificates. This is what happened in 2015 – when it was decided, that any domain with a “.local” ending couldn’t have a certificate anymore – cutting off any and all devices that only run in local WAN or LAN environments.
Read more about the problems in a local LAN/WLAN environment ..
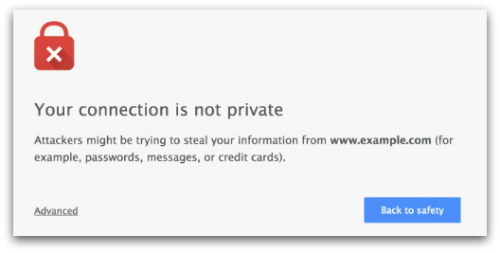
Now – of course there are (currently) ways to connect to services that haven’t been “verified”. But this results in scary browser warnings or require cumbersome installations and are not really acceptable – especially not for for common users. Who can tell if those work-around solutions are still available a few years down the road? Again – that would be up to a few browser manufacturers and not us.

What needs to be changed?
First and foremost – any critical technology should be created in a way that allows us, the Internet users, to have a say. None of our personal technical infrastructure should ever depend on the goodwill or benignness of a few companies or consortia. Especially not if it concerns our local LAN or WLAN environments or methods we could easily provide ourselves.
So here’s what we need to take control back:
Allow easy and automated installation of certain master certificates into browsers. Those master certificates are the foundation of the “trust” as explained above. If a browser knows a master certificate, it “trusts” whatever the master certificate has signed. However – this process could be misused and some folks could try to convince that their “version” of google.com is a trusted version. That obviously shouldn’t be allowed. So “easy import” certificates should only be valid for “.local” domains indicating that everything is for a WLAN / LAN only.
Allow alternative ways for “domain” validation. This is the most simple way of gaining trust – a domain validation (as opposed to Extended Validation) only indicates that the certificate belongs to a domain and the server using the certificate is actually rightfully owning the domain. Currently – a third party is necessary to verify the ownership of a domain. But that is completely unnecessary. Because the owner can prove ownership to the browser himself. By adding certain cryptographic elements to the name server. This is exactly the way email authenticity is managed (DKIM, SPF) – it should be acceptable for domain validation certification as well.
Allow self-signed certificates in a local environment without warning – this is an extension/alternative to the first thought. Whenever you deploy your own NAS or network devices, you can create a certificate that is “self signed” – in other words, it hasn’t been signed by any “certification authority”. However – browsers complain with big scary security warnings whenever they encounter a self signed certificate. While that is correct and desired on the open Internet – it doesn’t make sense in a local LAN/WLAN environment.
So – that’s it for the time being. We need to implement those changes in order to preserve the flexibility we all need in OUR Internet. Especially when it comes to LAN/WLAN services or devices that may not even be attached to the open Internet.
About the author:
Michaela Merz is an entrepreneur and first generation hacker. Her career started even before the Internet was available. She invented and developed a number of technologies now considered to be standard in modern web-environments. Among other things, she developed, founded, managed and sold Germany’s third largest Internet Online Service “germany.net” . She is very much active in the Internet business and enjoys “hacking” modern technologies like block chain, IoT and mobile-, voice- and web-based services.