I installed 550W of flexible solar panels on our Winnebago Outlook and they worked fine. However – everybody talks about air gaps nowadays – with ….
Category: english
We are installing a 550W solar system so that our Lithiums are always nicely charged.
We are converting our Class C RV to Lithium and solar to make it more capable for boondocking.
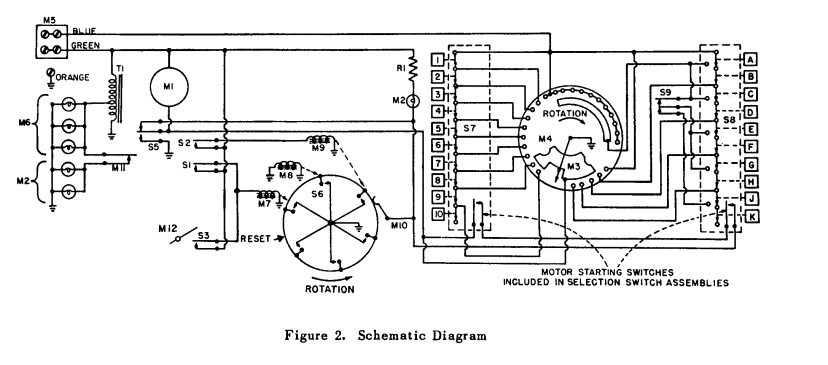
This is the story about building a evaporation pool chiller with sensors and a water return pump.
The principle idea of DOH holds a lot of promise if it is implemented in a respectful and cooperative way. The browser people are trying to bully us into their way of thinking. They disrespect our configurations, environments and settings and want to forward our sensitive data to some data center we have no relations with, we don’t know, have no contract, no service agreement and no way of contacting.
The ESP8266 is widely used in IoT applications. I have programmed a multitude of different sensors with it. And I almost found it’s limits – ….
Google has opened a Pandora’s box by proposing a W3C standard that would allow browsers to unilaterally freeze or even unload web-sites in/from the browser. ….
Battery endurance is a big issue with modern mobile devices. Who wants a phone that goes down in the middle of the day? But with ….
I developed web services before Larry or Sergey even thought about Google. From back then to now I have morphed from being a web-technology engineer ….
Back in the days, coders didn’t have the convenience of stackoverflow or GitHub. You wanted to do something, you had to “invent” it yourself. We ….